COMP 3000 2011 Report: Damn Vulnerable Linux
Part I
Background
Damn Vulnerable Linux (DVL) is a Slax-based, live-DVD Linux distribution designed as a sandbox for security testers. DVL intentionally includes outdated and exploitable software, providing its users with the necessary tools to practice security intrusion.[1]
OS Inheritance
Damn Vulnerable Linux is based on Slax[1], a popular bootable CD Linux distribution with a modular design. Slax provides a vast compact collection of pre-installed software and a well-designed user interface.[5]
Initial versions of DVL closely resembled Damn Small Linux, as the developers used the established techniques of DSL to provide small-sized (150MB) ISO releases.[4] The operating system also made use of the Linux 2.4 kernel in use by Damn Small Linux, as it provided additional security exploits that were fixed in later kernels.[4]
Development
Damn Vulnerable Linux was conceived and primarily developed by Dr. Thorsten Schneider, who integrated it into his university lectures on software security at Bielefeld University, Germany.[1] [3]
Schneider, then a member of the International Institute for Training, Assessment, and Certification (IITAC)[2], partnered with colleague Kryshaam of the French Reverse Engineering Team with the goal of creating a “plug-and-play system” that had “all the required tools installed” for training purposes, simply necessitating that the user to “run DVL in a virtual machine” to begin active learning.[4]
While initial releases maintained a close relationship to Damn Small Linux, the developers later decided to model the operating system after Backtrack 2.0. The latest release, Damn Vulnerable Linux 1.5: Infectious Disease, is downloadable as a 1.8GB ISO file.[6]
Target Audience
Damn Vulnerable Linux began as a functional tool for teaching students the importance of security. With its public release, Dr. Schneider and Kryshaam decided to continue this functionality, packaging a large collection of “tools, workbooks, text tutorials, and exploits” along with the operating system.[4] They later released their own mini-lectures on the main website, in the form of video tutorials. The first of these detailed how to cause a buffer overflow error.[4]
As with many Linux distributions, once in public domain DVL quickly found itself as the centerpiece of various community discussion groups. Users found alternative uses for the operating system, including as a secondary tool for testing the security exploitation and intrusion devices of Backtrack.[7]
Obtaining A Copy
The main website for Damn Vulnerable Linux has been offline for several months, reportedly having been taken offline due to German security laws.[9] It is possible to obtain an ISO copy of Damn Vulnerable Linux from Sourceforge.[6]
Installation / Startup
To install Damn Vulnerable Linux, make sure to obtan the most recent ISO file from Sourceforge.[6]
VMware Player Settings
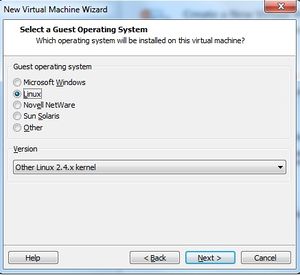
- Using VMware Player, Create a new virtual machine.
- Choose the option to install from disc image file, and browse to find the ISO location on your machine.
- When VMware prompts for the guest operating system, select ‘Linux’ and then ‘Other Linux 2.4.x kernel’ before proceeding.
- When naming the virtual machine, enter ‘DVL’ and select next.
- The default disk capacity and hardware settings are sufficient, so proceed through these stages without making any changes. Click Finish.
- Click enter to boot the system. This should take between 10 and 30 seconds.
- After the system successfully boots, login as ‘root’ with password ‘toor’.
- To switch from the command line to a graphical interface, type ‘startx’.


Basic Operation
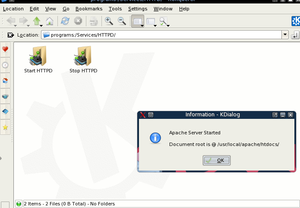
The graphical interface offered by DVL is very minimalistic and utilitarian. The desktop itself is populated solely with shortcuts to services, to provide a quick way to enable/disable various components - SSH, Apache, Mysql, PHP, etc. - or quick access to development environments such as C++ and Java.
Apache is an HTTP web server which is crucial to all web-based interactions within the operating system. When using Damn Vulnerable Linux, Apache must be started before HTTP, PHP, or MySql services become available.
The bottom menu panel contains a typical ‘start’ menu, as well as fast access to the terminal, two browsers (Firefox and Konqueror) and a text editor.
The ‘start’ menu further mirrors the icons on the desktop, organized in a ‘Services’ category, as well as providing shortcuts to the training material and other tools.
The overall organization of utilities is superb, as is the variety and quantity included. Integrated Development Environments (IDEs), applications that provide comprehensive features for software programmers, are included for many languages, ranging from Dr. Scheme to Eclipse and JEdit.
Damn Vulnerable Linux also includes disassemblers and debuggers, which are used heavily in breakpoint testing and reverse engineering. IDA free and Ollydbg number among those disassemblers and debuggers that are provided. DVL contains all the necessary development software that its users require.
Usage Evaluation
Damn Vulnerable Linux comes packaged with a large collection and assortment of tutorials, as well as their solutions. In this basic usage evaluation, I will examine the board51 package.
As web tutorials are accessed through localhost, to begin the tutorial necessitates first launching Apache, via the HTTPD shortcut on the desktop.
Board51 System
While there are many exploits detailed within DVL, this evaluation will characterize the operations of the board51 admin attack. As Damn Vulnerable Linux conveniently provides outdated software, this is an example of an attack that will not work on live pages - the error has since been fixed.
The 51 scripts software provide a forum, board and news system, and were previously found at www.laforge-groups.de. This security attack exploits the data storage system used by the software, primarily by retrieving the md5 hashes of user accounts and passwords from the storage file.
The Breach

By default, board51 stores the md5 hashes of user accounts in a public file, with read access available to everyone. To access this information, an attacker needs only browse to /boarddata/data/user.idx, and then proceed to decrypt the md5 hash.
Prevention
The administrator of a board51 website can prevent this attack by changing the privileges to the data folder and its files through chmod.
Overall Evaluation
Damn Vulnerable Linux is very effective at presenting a testbed for exploiting real cases of security flaws. It accomplishes its stated goal of teaching the importance of security, and displays the cruciality of reinforcing every component of software.
The ease-of-use is phenomenal, and the quantity of historical exploits from live software solidifies DVL as an essential learning tool for all security enthusiasts.
Part 2
Software Packaging
Slackware is RPM-based, meaning that software packages are all stored as an RPM Package Manager. By invoking rpm -qa, a list of installed RPMs is shown; within DVL, FPC (Free Pascal Compiler) is the only listed package. Free Pascal Compiler is an extensive RPM Package Manager that is often used in conjunction which Lazarus, which contains a full IDE.[13] The version of FPC used by Damn Vulnerable Linux is fpc-src-2.2.0-071105.i386.rpm, as reported by the following command:
rpm -qa
Lazarus contains a large host of utilities, separated into the run-time library (RTL), which contains units such as Unix, BaseUnix, and ShellAPI; and the Lazarus Component Library (LCL), which contains interface elements, such as buttons, forms, and text boxes.[11] While this is quite extensive, containing nine thousand files[12], it is the only package included in DVL. The operating system is relatively destitute compared to larger distributions such as Ubuntu, as it is focused heavily on a specialised programming environment.
The rpm command is very useful for adding and removing packages. The following parameters are highly useful:
To get a comprehensive list of all installed packages, as well as their version number and release date[14]:
rpm -qa
To uninstall a specific package[14]:
rpm -e <packagename>
To install a specific package[14]:
rpm -ivh <packagename>
To update a previously-installed package[14]:
rpm -Uvh <packagename>
The rpm command can also be used to request a list of installed files by a rpm, by invoking the following command:
rpm -ql fpc-src-2.2.0-071105
Major Package Versions
As Damn Vulnerable Linux is designed to be vulnerable, it makes heavy use of legacy code. This fundamental attribute is also evident within the packages included with the operating system. The authors do not make any effort to modify the source code of the original code, instead intentionally selecting packages that are either known to be exploitable themselves, or complement other exploitable software. It is with this in mind that each of the software packages are chosen to be included in the operating system.
| Software | Version(Date) | Most Recent Version | Command Used | |
|---|---|---|---|---|
| libc | 2.3.6 | 2.14 | /lib/libc.so.6 --version
|
|
| bash | 3.1.17(2005) | 4.2 | /bin/bash --version
|
|
| kernel | 2.6.20-BT-PwnSauce(2007) | 3.1.1 | uname -a
|
|
| GNU CoreUtils | 5.97 | 8.14 | /bin/ls --version
|
|
| procps | 3.2.7 | 3.2.8 | /bin/ps --version
|
|
| MySQL | 5.0.24a | 5.5.17 | mysql -V
|
|
| HTPPD | Apache 1.3.37 | 2.2.21 | httpd -V
|
|
| SSH | OpenSSH 4.4pl (2006) | 5.9 | ssh -V
|
|
| Konqueror | 3.5.3(2005) | 4.7.3 | konqueror -v
|
|
| Qt | 3.3.6 | 4.7.4 | konqueror -v
|
|
| KDE | 3.5.3 | 4.7 | konqueror -v
|
Note: The HTTPD version was likely chosen because of the significance of its version number among the target audience. Specifically, 1337 is usually inferred as numerical-representation of "leet", or elite.
Initialization
As a Slackware-based distribution, DVL uses BSD style init (as opposed to System V) to initialize the system. By reading /etc/inittab, it is apparent that the default runlevel is set to 3. inittab then tells the system to use /etc/rc.d/rc.S for initialization.
/etc/rc.d/rc.S begins by mounting /proc (/sbin/mount -v proc /proc -n -t proc).
It then starts udev, mounts sysfs, and checks for a forced filesystem check on the root filesystem (to see if fsck must be run due to an improper shutdown). If no fsck is required, it continues by setting the system time (from the hardware clock), and configures plug-and-play devices.
Then it proceeds to load any required kernel modules (for hardware such as the ethernet or sound cards), and configures runtime kernel parameters. Next, it checks for a forced fsck on any non-root filesystems, and then mounts non-root filesystems in fstab. It then enables swapping (/sbin/swapon -a), and cleans up temporary files and ensures the integrity of the temp folder (creating /tmp/.ICE-unix and /tmp/.Xll-unix if they are not present).
Next, it attempts to umount and remove any leftover files in /initrd, before creating a fresh utmp file. The MOTD is then set to reflect the current kernel level, and checks if there are any System V init scripts to be run at the current runlevel.
Source: inittab file
Due to the BSD-style initialization, the actual kernel modules are run from /etc/rc.d/rc.modules, and are explicitly loaded via modprobe[10].
As opposed to System V convention (which uses /etc/rc.d/rc(runlevel).d/ directories to house scripts), the primary script in DVL is run from /etc/rc.d/rc.M. This defines the system hostname, activates PCMCIA support, activates the firewall, starts network services, launches Inetd and OpenSSH, Bind, NIS, and NFS; starts system logging, smartd, cron, atd, MySQL, Apache, Samba, and any System V init scripts that have been added.[10]
Init Script Startup

The specific process executing order during initialisation is as follows:
Init(8) is run, resulting in:
/etc/rc.d/rc.M is executed, which in turn starts the following processes:
- /usr/sbin/syslogd: this is started by rc.M, by calling rc.syslog start
- /usr/sbin/klogd: syslog then starts klog if it is a SMP kernel
- inet1: this is started by rc.M
- dhcpcd: this is then started by inet1 if it is not already running, and set to eth0
- /usr/sbin/cupsd is started by rc.M, by calling rc.cups start
- /usr/sbin/crond is started by rc.M
- /usr/sbin/acpid: this is started by rc.M, by calling acpid start
- rc.M then calls the rc.slax extension
- /bin/sh: this is started by rc.slax
- /bin/bash: this is started by rc.slax
- /usr/libexec/mysqld: this is started by rc.M by calling rc.mysqld start
- /usr/sbin/gpm: this is started by rc.M, by calling rc.gpm start
References
[1] http://distrowatch.com/table.php?distribution=dvl
[4]http://web.archive.org/web/20090206193556/http://linux.com/articles/60267
[5]http://distrowatch.com/table.php?distribution=slax
[6]http://sourceforge.jp/projects/sfnet_virtualhacking/downloads/os/dvl/DVL_1.5_Infectious_Disease.iso/
[7]http://forums.hak5.org/index.php?showtopic=11389
[8]http://www.damnvulnerablelinux.com
[9]http://www.reddit.com/r/linux/comments/fid3k/damn_vulnerable_linux_is_gone/
[10]http://openskill.info/infobox.php?IDbox=1042
[11]http://wiki.lazarus.freepascal.org/Installing_Lazarus#Installing_using_rpms
[12]http://rpm.pbone.net/index.php3/stat/6/idpl/14565894/dir/other/com/fpc-src-2.2.0-071105.i386.rpm
[13]http://wiki.lazarus.freepascal.org/Overview_of_Free_Pascal_and_Lazarus
[14]http://www.linuxforums.org/forum/installation/2165-add-remove-packages-not-removing.html