Difference between revisions of "COMP 3000 2011 Report: Qubes beta 2"
| Line 48: | Line 48: | ||
===Basic Operation=== | ===Basic Operation=== | ||
Qubes runs a seemingly unmodified version of KDE graphical environment but unfortunately it is stripped down and contains only a few of the nice goodies that usually come along with that. The only difference that can be noted from a standard linux desktop running KDE is that it has an extra icon in the taskbar which can be used for managing app VMs. This app gives you all the options you need to manage your different VMs, you first name the VM, then you can choose whether or not this VM has access to the network, then you can transfer over to the advanced tab and set the maximum size of the VM. | Qubes runs a seemingly unmodified version of KDE graphical environment but unfortunately it is stripped down and contains only a few of the nice goodies that usually come along with that. The only difference that can be noted from a standard linux desktop running KDE is that it has an extra icon in the taskbar which can be used for managing app VMs. This app gives you all the options you need to manage your different VMs, you first name the VM, then you can choose whether or not this VM has access to the network, then you can transfer over to the advanced tab and set the maximum size of the VM and how much ram and cpu resources you would like to devote to it. | ||
The intended usage for this distribution is general productivity in a secure manner, so I decided to try installing some applications and putting them in different VMs in order to see how the VMs look to the user and how it deals with package management and updates inside the VMs | The intended usage for this distribution is general productivity in a secure manner, so I decided to try installing some applications and putting them in different VMs in order to see how the VMs look to the user and how it deals with package management and updates inside the VMs. | ||
Since this system is baed on fedora, it uses RPM packages and has the default package manager 'yum' with a kde frontend. It worked flawlessly, I installed a web browser and the open office suite and attempted to separate them into multiple VMs. Unfortunately this was too much for my system to handle running it in a VM and it politely displayed the message 'failed to start custom VM' and open office refused to open until I moved it back into the default VM. This is perfectly acceptable though given that my system just meets the requirements to run this OS natively so some hiccups are to be expected. | |||
===Usage Evaluation=== | ===Usage Evaluation=== | ||
Revision as of 22:16, 19 October 2011
Part 1
Background
Quebes is a very new Operating System based off the Fedora Linux OS combined with the Xen Hypervisor and X Windows System GUI aimed primarily at people dealing with confidential information but also anybody who is concerned about their computer security. The first beta was released on Apr 11, 2011 and the 2nd beta was released on Sep 19, 2011. It is actively being developed by Invisible Things Lab and it can be downloaded from here weighing in at a hefty 1.59gb for the install dvd.
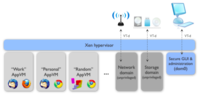
This OS is designed with the primary goal of being secure. It employs a highly unique and interesting technique to achieve this; it runs some of the system components in a virtual machine and it runs user applications in separate user defined virtual machines. This theoretically isolates applications and their memory contents. This makes it such that if one application misbehaves or is maliciously exploited it is unlikely to have an effect on other applications in a separate VM or the running system.
One of the truly revolutionary parts of this platform is the way that the GUI integrates the multiple VMs in order to make it as seamless as possible for the user to manage. The other majorly revolutionary part of this platform is the fact that it sandboxes parts of the system like networking for extra security.
Hardware Requirements
Minimum:
4GB of RAM 64-bit Intel or AMD processor (x86_64 aka x64 aka AMD64)
Intel GPU strongly preferred (if you have Nvidia GPU, prepare for some troubleshooting; we haven't tested ATI hardware)
10GB of disk (Note that it is possible to install Qubes on an external USB disk, so that you can try it without sacrificing your current system. Mind, however, that USB disks are usually SLOW!)
Fat SSD disk strongly recommended
Additional criteria
Intel VT-d or AMD IOMMU technology (this is needed for effective isolation of your network VMs)
If you don't meet the additional criteria, you can still install and use Qubes. It still offers significant security improvement over traditional OSes, because things such as GUI isolation, or kernel protection do not require special hardware.
Note: We don't recommend installing Qubes in a virtual machine! Note: There is a problem with supporting keyboard and mouse on Mac, and so Mac hardware is currently unsupported (patches welcomed!)
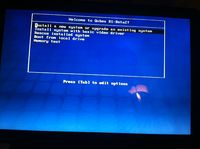
Installation/Startup
Install is pretty standard and straightforward compared with other OSs and Linux distros I am installing on a 2011 MacBook pro (which I know is unsupported, but let's see how it goes…) unfortunately I am going to be installing to an external hard drive so I will not be able to give a true performance evaluation.
I ran into my first issue very quickly which was that I did not read there release notes for beta 2 and I discovered that the installer does not support my macbook pro keyboard but this was quickly remedied by plugging in a USB keyboard. I decided to skip the disk check and then I was asked to partion my drive and set a time zone. I chose to encrypt my hard drive because it would feel a little hypocritical not to with such a secure OS.
After that the install failed, let this be a lesson to you to check your disk if you want to potentially save some time. I redownloaded the imagine and went through the installation again, now after completing the installation my mac was unable to boot from the USB hard drive, so I gave the usb hard drive a try on a PC as well as through REefIt mac software and it wouldn't boot. So I gave a native installation a try, I wiped my bootcamp partition off my macbook and I installed Qubes in its place. To my disappointment it still would not boot and REefIt could see it but it would just say "No Operating System Present, Insert Bootable Disk and Press Enter To Continue".
So I gave up and I installed Qubes in a VM which is incapable of showing its true power and is not recommended but I was left with no options to get this OS up and running. I used VMWare Fusion to run it.
Upon the first boot I was greeted with a nice welcome screen that walked me through creating a user account and asked me how I wanted to manage my VM bottles. It gives you 3 options at this point, you can have it automatically create the default app VMs (which is what most basic users want), you could manually specify the app VMs (which could be useful for setting home/work bottles, etc) and then there's the option not to create any VMs which is not recommended.
After these simple steps you will end up at the standard KDE login screen.
Basic Operation
Qubes runs a seemingly unmodified version of KDE graphical environment but unfortunately it is stripped down and contains only a few of the nice goodies that usually come along with that. The only difference that can be noted from a standard linux desktop running KDE is that it has an extra icon in the taskbar which can be used for managing app VMs. This app gives you all the options you need to manage your different VMs, you first name the VM, then you can choose whether or not this VM has access to the network, then you can transfer over to the advanced tab and set the maximum size of the VM and how much ram and cpu resources you would like to devote to it.
The intended usage for this distribution is general productivity in a secure manner, so I decided to try installing some applications and putting them in different VMs in order to see how the VMs look to the user and how it deals with package management and updates inside the VMs.
Since this system is baed on fedora, it uses RPM packages and has the default package manager 'yum' with a kde frontend. It worked flawlessly, I installed a web browser and the open office suite and attempted to separate them into multiple VMs. Unfortunately this was too much for my system to handle running it in a VM and it politely displayed the message 'failed to start custom VM' and open office refused to open until I moved it back into the default VM. This is perfectly acceptable though given that my system just meets the requirements to run this OS natively so some hiccups are to be expected.
Usage Evaluation
With the goal being security, this distribution definitely accomplishes that in a way that provides different levels of security depending on the computing knowledge of the user or administrator. It appears to be aimed at advanced computer users especially given that the website makes little effort to explain the basic concepts behind a VM which the whole OS is based on. From my experience this distribution need not only be aimed at advanced users because it provides a much higher level of security than a normal OS in some fields and unless the user wants to manage it, it is completely transparent.
Note: This is beta software and it might just not be aimed at regular users for this reason.
From the start the system will setup VMs for the user, the most important of which being the system VMs; it creates one for the networking components of the OS and one for the GUI. Then if the user is advanced enough and understands the advantages they can manually separate apps into the 2 VMs with ease and install new ones into the different app