COMP 3000 2011 Report: CAINE
Part 1
Background
CAINE, which stands for Computer Aided INvestigative Environment, is a Linux environment whose main purpose is to provide specific investigative and reporting tools that would prove useful to a forensic scientists.<ref name = "CAINE">CAINE-Live Website (Last accessed October 19, 2011).</ref> This Linux environment was originally created in Italy and is currently being managed by Mr. Nanni Bassetti (Website in Italian).
Something to consider before diving into what CAINE is used for is to get a quick understanding about the four step process model put in place by the U.S Department of Justice with regards to digital forensics.<ref name = "DigiForen">Digital Forensics - The Enhanced Digital Investigation Process Model (Last accessed October 14th, 2011).</ref>
The four stages of digital forensics:<ref name = "DigiForen"/>
- Collection deals with evidence finding, recognition, collection, and some early documentation with details about the evidence.
- Examination has the scientist sifting through the already collected evidence with different software. The goal is to find out where the evidence came from and if it is significant. It also may reveal previously unknown information about the piece of evidence with in-depth examination.
- Analysis happens after the examination process has deemed a piece of evidence significant enough. By piecing together information gained through the examination stage, the scientist will decide just how relevant the evidence is to the current case.
- Reporting, the final stage, is writing a simple report touching on the examination process and giving a detailed look at all the relevant information gathered through Examination and Analysis that will hopefully help the case in some way.
The design goals that CAINE strives to achieve are as follows:<ref name = "CAINE"/>
- A diverse environment that gives the flexibility and all the tools necessary to the forensic scientist during all four stages of the digital forensics.
- A user-friendly GUI.
- A tool which provided a simple, semi-automatic solution for reporting.
Obtaining CAINE is quite simple. The main website hosts the under 700MB .ISO file directly. The direct download link to CAINE can be found here. There is also an 865MB file that is available for netbooks as well. It can be found here.
Finally, CAINE was created with pieces from Ubuntu 10.04 and Remastersys created by Tony Brijeski<ref name = "CAINEFAQ">CAINE FAQs (Last accessed October 17th, 2011)</ref>
Installation/Startup
Initialization
Upon starting up CAINE for the very first time. Something to note is that the installation doesn't actually start upon first boot-up. Since CAINE's .ISO file is a Live CD, it has the full operating system (OS) with pre-configured software and settings<ref name = "LiveCD">The Magic of Live CDs (Last accessed October 17th, 2011).</ref>. For the sake of seeing how the installation process works, though, I will go through and ensure that CAINE is actually installed the HDD.
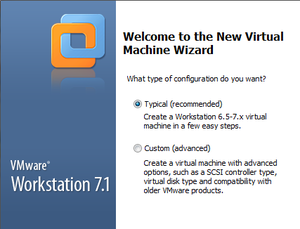
The software that was used to virtualize CAINE was VMWare Workstation, specifically version 7.1.4 build-385536. [Figure 1]
The specifications of the virtual machine are as follows:
- Typical install (Creates a Workstation 6.5-7.x virtual machine)
- Selected the Caine 2.5 .ISO file.
- Selected a Linux OS with type "Other Linux 2.6.x kernel".
- Allocated 20GB for the virtual machine and 512MB of RAM.
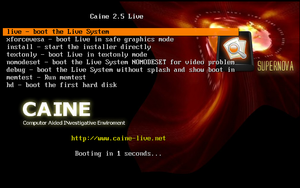
CAINE booted up with no initial problems with a boot screen full of options. [Figure 2]
The options include:
- Booting the Live System (which is chosen if no action is taken in 10 seconds).
- Low-graphics mode for lower-end machines.
- Command to start the full-install right away.
- Text only mode.
- Video diagnostics command.
- Debug mode.
- Memory diagnostics command.
- Boot from the first HDD.
NOTE: At this point, do not attempt to restart the virtual machine. The system will hang and you will have no choice but to force close the virtual machine and re-open.
After either selecting the Live Boot or waiting for 10 seconds, the desktop will be displayed. [Figure 3]
Installation
Note: All choices made in the test install will be written in parantheses.
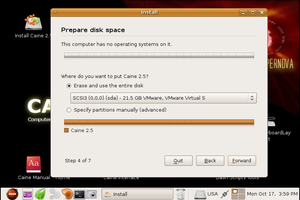
After clicking on the Install CAINE 2.5 icon, the user is given the option of selecting a language (English). The installation then initializes the clock to some server's clock, and asks for the user to select the time zone by region (Canada) and Time Zone (Canada Toronto). Afterwards, the user is prompted to selected a keyboard, with the suggested option being USA (USA). Next, the user is prompted to specify a partition in which to install Caine 2.5 on (Erase and use the entire disk) [Figure 4]. The user is then prompted to enter their name, username, password, and the name of the computer. Once this is complete, the user is shown a review of all the choices they have made with a final message stating that all these choices will be applied to the disk upon clicking "Install".
The CAINE OS will now begin installing to the HDD. Once the installation is complete, the user will be prompted to either restart or continue with manual configurations. Now the virtual machine can be properly restarted without needing to force quit the virtual machine. Upon restarting, the user is asked to choose either the OS, or the memory diagnostics tool. Something to note is that the OS that is available isn't called "CAINE", it says "Ubuntu, with Linux 2.6.32-33-generic". This most likely comes from the fact that CAINE was born from Ubuntu and most likely shares a lot of its kernal.
Basic Operation
(Being a beginner when it comes to all forms of forensics, whether field, digital, or documentation, I will do my best to give an appropriate overview of CAINE.)
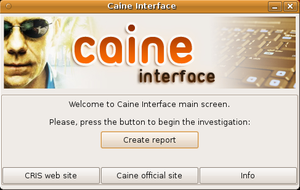
Since CAINE was intended specifically for people who work in the digital forensics field, I started looking around the OS for some of the software the developer said could help in all stages of digital forensics. Luckily, right on the desktop was something called "Caine Interface" which seemed to be the hub that linked to all things that have to do with CAINE. [Figure 5]
Upon clicking on it, I was greeted with a slick looking message box that allowed me to create a report. After clicking on it, I was prompted to enter the name of the case and the name of the lead investigator. Afterwards, a handful of tabs popped up with many different programs available. The main types seemed to be disk image file creating and testing to ensure nothing's been corrupted, and different methods of analyzing said image.
One of the programs I tried was AIR, which stands for Automated Image & Recovery. This program is used to create forensic disk images as well as recover them<ref name = "AIR">Automated Image and Restore (Last accessed October 18th, 2011)</ref>. Since CAINE runs on a Live-CD, the ability to create a forensic disk image quickly of a computer that is in the possession of investigators would be quite useful.
After looking at AIR, I clicked on the tab that led to a lot of different analysis tools. One of the more interesting ones was software called Stegdetect. According to the program itself, its purpose is to search through a folder containing .JPG files to determine if there are any steganographic (secret) content to the image, whether it be a hidden image, data that is secretly attached to the picture, a hidden message (etc).
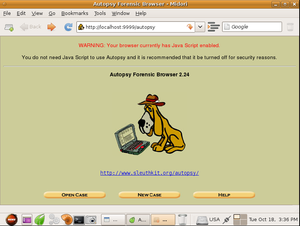
The main GUI for digital forensics analysis was the Autopsy program. It is useful if the investigators have an image file of an entire disk or partition of a computer that they wish to search through.
The "Autopsy 2.24" icon opened a program that first, launched in a command window which afterwards automatically opened a browser window with the program ready to be used. This software allows for a user to create a new case or open a previously created one. [Figure 6] Upon creating a new case, the software asks for the case name, a short description, and a list of all the investigators that are assigned to this case. Once this has all been filled out, the program then asks for a host to be created. This host is the computer that is currently under investigation. The program then asks for the name of the host computer and a short description. Also, optionally, it asks for a specified timezone, timeskew adjustment (to compensate for how much or little the computer is off from another computer's time), and a hashtable for known good and bad files. Once this is complete, the program asks for an image file, which is interpreted as a filepath. Then it asks if this file path points to a disk or partition, and then finally how to extract the files, either by moving, copying, or simply linking to them.
At this point, I did not have an image file on hand to investigate, so I could not delve further into this program, but from reading through the provided help manual I was able to determine that once an image file has been loaded in, there are some commands that can be used to search for keywords inside the files themselves.
Usage Evaluation
CAINE, I believe, being targeted to people in the digital forensic profession makes a very good case for being a viable solution for digital forensics. An easy install coupled with the option of using the Live-CD desktop gives the user enough options depending on the situation. As I said earlier, the Live-CD would be a great option if they needed to quickly make an image file of a computer that may be partaking in illegal activity.
The choice of having all relevant software in one convenient place was a professional choice. This allows people who may not be too familiar with Linux, or even computers to quickly get access to the software they need to do their job.
From what I have seen of the software provided, CAINE seems to deliver adequately on its promises of providing all tools necessary for all stages in the digital forensics process. Although I am not actually a digital forensic scientist, I was able to thoroughly test all the software. It seemed as though everything that a digital forensic scientist would need was available and easy to use.
In closing, I would recommend CAINE to any forensic scientist who wants a portable, easy-to-use operating system with some great software to help them do their job.
Part II
Software Packaging
Main Software Pack
As mentioned above, CAINE Linux is designed to meet the needs of digital forensic scientists. This goal is mostly met by the software that is provided with CAINE. Before delving into the package structure, taking a quick look at the initial forensic software given with this OS is a good idea. As also spoken of beforehand, CAINE comes with a program called "CAINE Interface", which is simple little UI that contains all of the forensic software that is given to the user via this distribution. With the most important software all packaged together in this intuitive interface, it shows CAINE's dedicated to showing users that it comes as advertised.
Package Managers
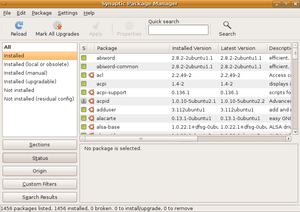
CAINE also uses the package manager dpkg, which is a package manager originally created for use in the Debian Linux OS. It deals with .deb package files. Dpkg is a terminal launched utility that is used to install, remove, or provide the user with information about packages.<ref name = "Dpkg">Wikipedia Entry for Dpkg (Last accessed November 12th, 2011)</ref> After some searching, it was found that there is another package manager that comes with CAINE, Synaptic Package Manager. This utility is a graphical UI that seems a lot more user friendly than its counterpart, dpkg. Provided below will be both ways to achieve a packaging goal, whether with dpkg, or with Synaptic Package Manager.
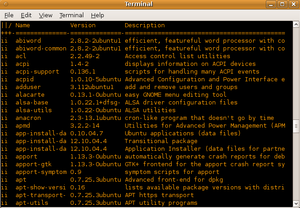
Listing Packages
To get a list of packages installed on CAINE using dpkg, all the user needs to do is open a terminal and type dpkg --list. This will provide the user with the entire alphabetical list of installed packages, their version number, and a short description of each package. In order to actually see all of the packages, when using the --list command, ensure that in the terminal options, the scrollback is either set to a large number or to unlimited, because, at least in CAINE, there are a lot of packages to be displayed. [Figure 7] If the user prefers a graphical interface, simply open Synaptic Package Manager (ensuring that the user has administrative access), and check the box on the left of the window that says "Installed". [Figure 8]
Adding & Removing Packages
Using dpkg, the user must move the directory with the package their either want to install or remove using the terminal, and type in either dpkg --install <package-name>.deb or dpkg --remove <package-name>.deb respectively. This is pretty self-explanatory for removing packages, but for adding them, the user must manually provide them from some external means if they wish to install a new package.
On the contrary, using Synaptic Package Manager makes this process a lot easier. To add new packages, the user can simply check the box "Not installed" and be given a list of packages they don't have installed on their computer. After selecting one or more packages, click the apply button at the top to proceed to automatically download and install the selected packages. Removing packages is also quite simple. Check the "Installed" button, then right click on the package that will be removed and select "Mark for removal". Just the same as adding, click the apply button and the program will proceed to remove the selected packages.
Software Catalog
Using Synaptic Package Manager, over 30,711 packages were found, and 1456 were already installed. According to this comparison, Ubuntu has the most available packages out of any distribution by a fair margin. The number given was 37,000.<ref name = "Comparison">Comparison of Linux Distributions (Last accessed November 12th, 2011)</ref> After looking at a lot of different distributions, it seems that CAINE Linux has a very large amount of packages available to it. This could be because it was created from Ubuntu, originally, and therefore a lot of packages made for Ubuntu are compatible with CAINE.
Major Package Versions
Here is a list of some of the major packages, their version numbers in comparison to the most stable release, as well as other relevant info.
Shell
The shell being looked at is bash, due to its common use amongst almost all flavours of Linux.
- bash
- Installed version: 4.1-2
- Latest version: 4.2
- Upstream Source: http://www.gnu.org/software/bash/bash
- Other info: The installed and latest version are the close, so it appears that no major changes were made to the package. Since bash is an important and widely used shell in Linux, it wouldn't make sense to modify at all. This is most likely why an almost up-to-date version is installed. The only reason I could think of why it isn't fully updated is an oversight by the distributor. CAINE is used more for its graphical forensic software and not for shell commands.<ref name = "CAINE"></ref>
Web Browser
CAINE Linux came loaded with only one web browser. This is the reason this package was chosen to be looked at below.
- Midori
- Installed version: 0.2.2-1
- Latest version: 0.4.2
- Upstream Source: http://www.twotoasts.de/index.php?/pages/midori_summary.html
- Other info: Web browser. There seems to be a wide gap in in the different versions. Since some of CAINE's software runs through a web browser, unless there appears to be a compatibility error, the distributor most likely doesn't feel they need to update.
Kernel
The Linux kernel, possibly the most important item of interest in terms of packaging. If the kernel has been changed at all, it could mean that the OS would behave much differently than the Linux that we are used to.
- Linux Kernel
- Installed version: 2.6.32-33-generic
- Latest version: 3.1.1
- Upstream Source: http://www.kernel.org/
- Other info: The "generic" in the installed version would lead to believe that nothing has been modified in the kernel from its Ubuntu origins. Very recently updated.
Packaging
A very common packaging tool was chosen to be looked at. Without something like this, it would be very difficult to manage packages at all.
- dpkg
- Installed version: 1.15.5.6
- Latest version: 1.15.7.2
- Upstream Source: http://packages.debian.org/search?keywords=dpkg
- Other info: Like the Bash installation, these version numbers are very close, so I don't assume any changes have been made. It was, again, probably just an oversight not to update it fully.
User Applications
Below are some user applications that would be important to CAINE users. These include: A bluetooth device for secure, convenient usage, software that is able to look at damaged media and be able to discover what is actually stored on it, and a simple word processing tool that can be used to quickly jot down important information. These three pieces of software would be very useful for a forensic scientist to help with his/her job.
- Bluez
- Installed version: 4.60-0
- Latest version: 4.96
- Upstream Source: http://www.bluez.org/download/
- Other info: Bluetooth. Again, not modified and updating is probably just an oversight of the distributor.
- DvDisaster
- Installed version: 0.72.1-1
- Latest version: 0.72.3
- Upstream Source: http://dvdisaster.net/en/
- Other info: Important software for CAINE as it is used to read old/scratched discs that are normally unreadable.<ref name = "DvD">DvDisaster Home Page (Last Accessed November 13th, 2011)</ref> Shows no signs of being modified at all. Very close to up-to-date, willing to bet that since this is such an important piece of software, the next version of CAINE Linux will make sure to make updating DvDisaster a priority.
- AbiWord
- Installed version: 2.8.2-2
- Latest version: 2.8.6
- Upstream Source: http://www.abisource.com/
- Other info: Not modified from what I have tested, and since there have only been minor updates in the past few updates, either an oversight, or just didn't bother updating.<ref name = "Abi">Abiword Release Notes(Last Accessed November 13th, 2011)</ref>
Software/GUI Creation
Below are two pieces of software that are quite useful for computer scientists and forensic scientists alike. Having some programming knowledge would be quite valuable if a forensic scientist needs to crack through a locked PC of a cyber criminal.
- GTK+
- Installed version: 2.20.2-1
- Latest version: 3.0
- Upstream Source: http:http://www.gtk.org/
- Other info: It is not uncommon for an OS to require an older version of GTK+, so this could be the case with CAINE Linux.<ref name = "GTK">GTK+ Download Page (Last Accessed November 13th, 2011)</ref>
- gcc
- Installed version: 4.4.3-1
- Latest version: 4.6.3
- Upstream Source: http://gcc.gnu.org/
- Other info: Updates have come in the last year<ref name = "gcc">GCC Website(Last Accessed November 13th, 2011)</ref>, so this will probably be updated in the next release of CAINE Linux.
System Tools
A very useful tool for checking for memory errors. Would be a good starting check for a forensic scientist to look at if they receive a damaged PC. If the computer won't start up, and it is only due to bad memory, this software could could help get things moving quickly.
- memtest86+
- Installed version: 4.00-2
- Latest version: 4.20
- Upstream Source: http://www.memtest.org/
- Other info: Again, not modified and updating has been most likely an oversight, as there have been two version jumps in the last two years (4.10 in 2010, and 4.20 in early 2011).<ref name = "memtest86+">Memtest86+ Download Website(Last Accessed November 13th, 2011)</ref>
Initialization
As is a typical Linux startup<ref name = "Startup">6 Steps of a Linux Startup(Last Accessed November 14, 2011)</ref>, CAINE Linux will first start up with the BIOS, which then calls the Master Boot Record (MBR). The MBR lets me choose the OS, OS in recovery mode, or memtest86+.
The kernel will then run all system required initializations, such as mounting devices, running drivers, and memory managers.<ref name= "WikiStartup">Wikipedia Article on Linux Startup(Last Accessed November 14th, 2011)</ref>. Then, /sbin/init will run and choose the default run level. Since CAINE Linux originally came from Ubuntu, it has thrown away the /etc/inittab file for choosing a run level.<ref name = "Noinittab">Ubuntu Forum - Talking About Lack of Inittab(Last Accessed November 14th, 2011)</ref> After some searching, I was able to find that the default run level is set to 2 from the /etc/init/rc-sysint.conf file.
Startup Programs
Found in the /etc/rc2.d directory.
When starting up, one of the most important daemons will launch. This is the APM (Advanced Power Management) daemon. This will run in the background from startup till shutdown, ensuring that power has been allocated properly. If this were to malfunction, the computer may accidentally give too much power (possible risk to hardware) or too little power (possible risk of data loss from an improper shutdown). Another important daemon is the Fan Control (Fan speed regulator) daemon. Again, this runs in the background, and is there to ensure the fan is spinning the right speed for any given task(s). Without proper fan cooling, as with the power management, this could result in damage to the hardware due to overheating.
Next, is a startup program that not only can help the user, but many others as well. The Kernel Loops startup program sends kernel crash error reports to the kernelloops.org website for use by Linux kernel developers. A crash that is born from some strange little error in the kernel code can be pinpointed easier with the help of these crash reports. If all goes well with the boot, the Grub Common will report a successful boot. If not, GRUB displays the boot menu at the next boot if the previous boot has failed.
Another interesting startup program is the Hotkey Setup. This allows laptops with built in hotkeys to function properly. Unfortunately, this currently has no use in desktops.
References
<references />