Report: TAILS: Difference between revisions
| (51 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
== PART 1 == | == PART 1 == | ||
== Background == | == Background == | ||
<p> | <p> | ||
The distribution is known as The Amnesic Incognito Live System (TAILS). The goal of the distribution is to provide anonymity for the user and thus targets any consumers that require a higher level of privacy when using the | The distribution is known as The Amnesic Incognito Live System (TAILS). The goal of the distribution is to provide anonymity for the user and thus targets any consumers that require a higher level of privacy when using the Internet and do not want to leave traces of their activity on the host file system. TAILS is an extension of the Debian GNU/Linux distribution system. It is open source but the project started being developed by developers at boum.org although I was unable to find any specific developer names. | ||
</p> | </p> | ||
<p> | <p> | ||
To achieve online anonymity, TAILS uses the Tor Network. The Tor Network is an open network that is accessible through free software. Tor is designed to make it difficult for anyone to trace your | To achieve online anonymity, TAILS uses the Tor Network. The Tor Network is an open network that is accessible through free software. Tor is designed to make it difficult for anyone to trace your Internet traffic. It uses a network of virtual tunnels to protect the user from “traffic analysis” (eavesdropping, IP spoofing, ARP spoofing, etc...). To combat these attacks it sends your data packets as multi-hop circuit of relays. Each relay only knows the address of the relay that provided the data and the relay it will provide the data too. This effectively erases the track back to the sender. Any eavesdropper will only be able to trace the message back to the relay before. One drawback is that the Tor network does not encrypt data from relay to relay only from the sender to the first relay and from that relay back to the sender. This prevents the eavesdropper from being able to view your data at the first relay but does not prevent them from viewing your data at other relays. Although the onus is on the website the user is communicating with to provide the end-to-end protection TAILS does provide this protection when using IRC or Email through software that comes with the system. Another drawback is that most if not all modern web browsers use JavaScript, Adobe Flash and cookies, these have been proven to occasionally bypass the anonymity feature. To combat this TAILS provides its own web browser based of Firefox called Iceweasel. Unfortunately some sites will not work with it due to its limitations. | ||
</p> | </p> | ||
| Line 16: | Line 15: | ||
<p> | <p> | ||
TAILS can be obtained for free from the | TAILS can be obtained for free from the Internet. The latest version is 0.8.1 and it was released on October 16th, 2011. It downloads as an ISO image of 579 Mb in size. The home website for TAILS has an interesting feature where it allows the user to verify that the ISO they downloaded is authentic as the genuine version is encoded with a cryptographic signature. The user can either do this through a check through Firefox, using an add-on, or through software known as Gpg4win which is essentially an encryption and decryption software. This just shows the level of commitment the developers have to user privacy and security. | ||
</p> | </p> | ||
| Line 22: | Line 21: | ||
<p> | <p> | ||
Once the user has downloaded the ISO image they will need to make the USB or CD key | Once the user has downloaded the ISO image they will need to make the USB or CD key boot from that ISO. I used the USB approach and used the Universal USB Installer software (version 1.8.6.8). The software provides you a main window where the user selects the type of distribution, the location of the ISO file and selects the USB key drive letter from a drop down menu. The user can also format the key during the setup process. After creating the USB key, users simply make the host PC boot to the USB upon startup. You will be presented with a boot menu where you can select your preferred language. The distribution system then loads the desktop UI and TAILS automatically launches an Iceweasel session window and tests the TOR connection. | ||
</p> | </p> | ||
| Line 30: | Line 29: | ||
<p> | <p> | ||
The actual start-up of the distribution system from the USB key was very fast. The load time was approximately 30-45 seconds | The actual start-up of the distribution system from the USB key was very fast. The load time was approximately 30-45 seconds after choosing the language at the boot menu. As TAILS is meant to run as a Livedistro system I did not use any virtualization software to get it running (although the option is there if you so choose) and as such do not have a screen shot of the actual loading process. | ||
</p> | </p> | ||
== Basic Operation == | == Basic Operation == | ||
| Line 40: | Line 38: | ||
<p> | <p> | ||
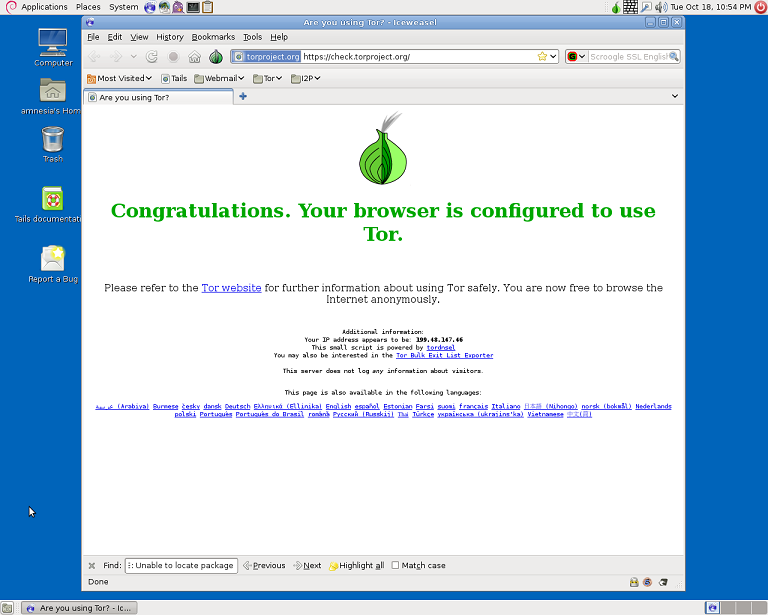
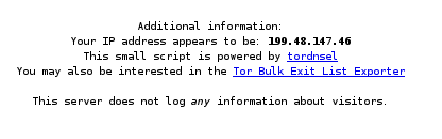
As TAILS first runs a web browser to TOR to test the network connection it provides you with the falsified IP address your system uses when on the network. Checking the TAILS distribution using ifconfig it showed that the IP addresses did not match up. | As TAILS first runs a web browser to TOR to test the network connection it provides you with the falsified IP address your system uses when on the network. Checking the TAILS distribution using /* ifconfig */ it showed that the IP addresses did not match up. | ||
</p> | </p> | ||
| Line 63: | Line 61: | ||
• Choose a new identity to use: Tears down all current circuits and creates new ones. Your route is modified into a new one. | • Choose a new identity to use: Tears down all current circuits and creates new ones. Your route is modified into a new one. | ||
<p> | |||
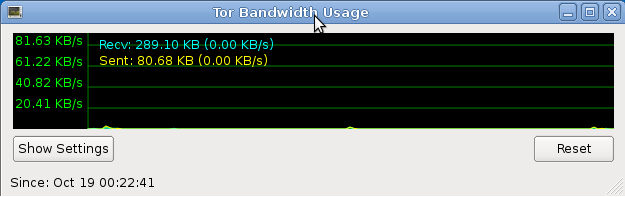
• View the bandwidth graph: This allows the user to check the current bandwidth usage on their circuit. | • View the bandwidth graph: This allows the user to check the current bandwidth usage on their circuit. | ||
</p> | |||
<center>[[File:bandwidth.png]]</center> | <center>[[File:bandwidth.png]]</center> | ||
| Line 70: | Line 71: | ||
• Connect through a bridge: If your ISP prevents you from using the Tor network you can “bridge” into the Tor network using Vidalia by going to the settings, network and then selecting the “My ISP blocks connections to the Tor network” checkbox. This will bring you to a form to add a Tor bridge as an entry point. | • Connect through a bridge: If your ISP prevents you from using the Tor network you can “bridge” into the Tor network using Vidalia by going to the settings, network and then selecting the “My ISP blocks connections to the Tor network” checkbox. This will bring you to a form to add a Tor bridge as an entry point. | ||
<p> | |||
• Setting up a Tor relay: Vidalia gives the user the option of setting themselves up as a Tor relay to help the Tor network. | • Setting up a Tor relay: Vidalia gives the user the option of setting themselves up as a Tor relay to help the Tor network. | ||
</p> | |||
<p> | |||
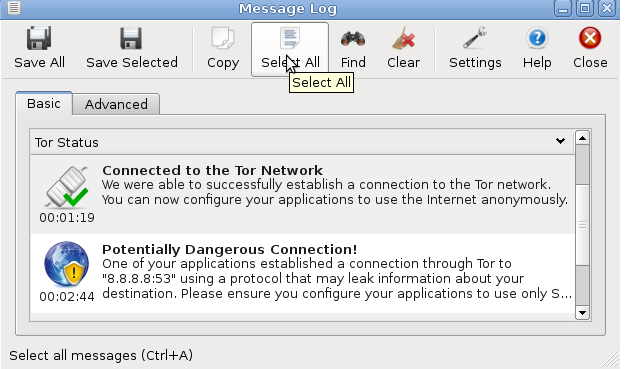
• Message Log: Acts as an event viewer for the Tor network. Displays messages such as if the Tor software is running and if there is a dangerous connection | • Message Log: Acts as an event viewer for the Tor network. Displays messages such as if the Tor software is running and if there is a dangerous connection | ||
</p> | |||
<center>[[File:message_log.png]]</center> | <center>[[File:message_log.png]]</center> | ||
| Line 96: | Line 102: | ||
== PART 2 == | == PART 2 == | ||
== Software Packaging == | == Software Packaging == | ||
<p> | <p> | ||
As TAILS is | As TAILS is modelled off Debian GNU/Linux distribution it uses the Debian (*.deb) packaging format for its software. | ||
TAILS comes preloaded with some of the usual software packages such as OpenOffice.org, Iceweasel and GNOME-terminal. In total TAILS comes preloaded | |||
usual software packages such as OpenOffice.org, Iceweasel and GNOME-terminal. In total TAILS comes preloaded | |||
with 1096 packages as is shown by the Synaptic Package Manager main window, which is a front end | with 1096 packages as is shown by the Synaptic Package Manager main window, which is a front end | ||
GUI to dpkg. TAILS uses the Advanced Packaging Tool (APT) system to manage the installation and removal of software. | GUI to dpkg. TAILS uses the Advanced Packaging Tool (APT) system to manage the installation and removal of software. | ||
It is a front end user interface for the dpkg package utility | It is a front end user interface for the dpkg package utility. Where dpkg is used on individual packages | ||
the apt tools in the apt package (such as apt-get) manage the | the apt tools in the apt package (such as apt-get) manage the relations between the packages. | ||
I primarily used the man page for dpkg to find the necessary information. | I primarily used the man page for dpkg to find the necessary information. | ||
</p> | </p> | ||
<p> | <p> | ||
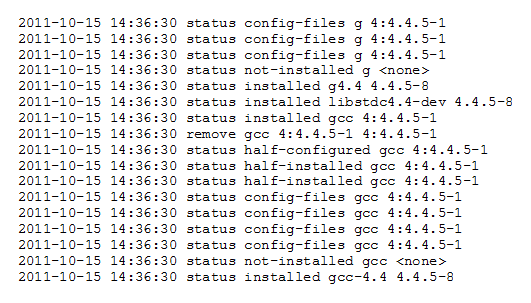
To get a list of the packages that are installed the user can search the /var/log/dpkg.log file. This will provide the | To get a list of the packages that are installed the user can search the /var/log/dpkg.log file with the following command: /* more /var/log/dpkg.log */ | ||
user with a list of when a certain software package was installed, removed or updated. The user can also type dpkg -l at the | </p> | ||
<p> | |||
This will provide the user with a list of when a certain software package was installed, removed or updated. The user can also type /* dpkg -l */ at the | |||
commnd prompt. This will provide the user with a list of installed packages in alphabetical order as well as the access rights | commnd prompt. This will provide the user with a list of installed packages in alphabetical order as well as the access rights | ||
associated to them. | associated to them. | ||
| Line 121: | Line 127: | ||
<center><u>Figure 8: Sample Output of dpkg.log File</u></center> | <center><u>Figure 8: Sample Output of dpkg.log File</u></center> | ||
<p> | <p> | ||
| Line 133: | Line 135: | ||
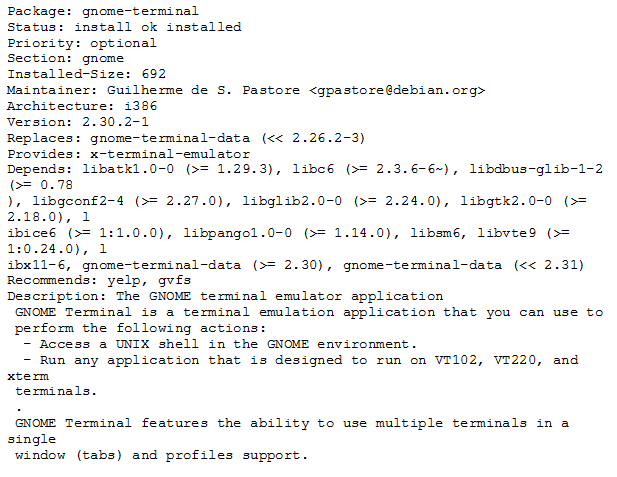
<center>[[File:status_output.png]]</center> | <center>[[File:status_output.png]]</center> | ||
<center><u>Figure | <center><u>Figure 9: Sample Output of /var/lib/dpkg/status File</u></center> | ||
<p> | <p> | ||
To add and remove packages the user would use the apt-get package mentioned earlier. To insatll a package | To add and remove packages the user would use the apt-get package mentioned earlier. To insatll a package | ||
the user would type the following command: apt-get install [package_name]. The user can specify more | the user would type the following command: /* apt-get install [package_name] */. The user can specify more | ||
than one package at a time. To remove packages the user would type the following command at the command | than one package at a time. To remove packages the user would type the following command at the command | ||
line prompt: apt-get remove [filename]. As with install the user can specify more than one filename.A set | line prompt: apt-get remove [filename]. As with install the user can specify more than one filename. A set | ||
of options are available in conjunction with these commands such as, -d which specifies to only download | of options are available in conjunction with these commands such as, -d which specifies to only download | ||
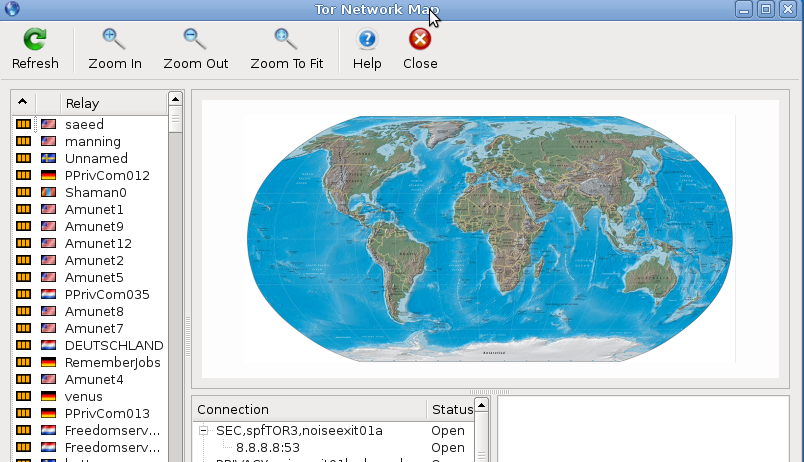
the package. Unfortunately for TAILS this function does not seem to work. There is always an error: | the package. Unfortunately for TAILS this function does not seem to work. There is always an error: | ||
| Line 147: | Line 149: | ||
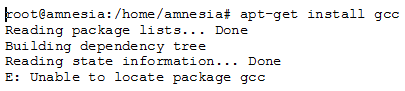
<center>[[File:apt_get_error.png]]</center> | <center>[[File:apt_get_error.png]]</center> | ||
<center><u>Figure | <center><u>Figure 10: apt-get install Error</u></center> | ||
<p> | <p> | ||
| Line 156: | Line 158: | ||
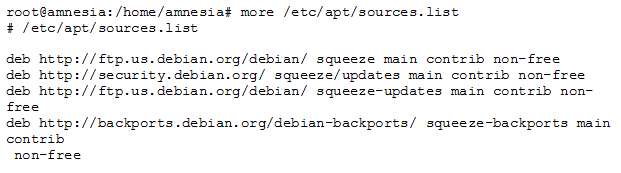
<center>[[File:sources_list.png]]</center> | <center>[[File:sources_list.png]]</center> | ||
<center><u>Figure | <center><u>Figure 11: sources.list File Output</u></center> | ||
<p> | <p> | ||
To install the packages I had to use the Synaptic Package Manager utility that comes available with TAILS. This | To install the packages I had to use the Synaptic Package Manager utility that comes available with TAILS. This | ||
is a front end graphical interface for apt that gives a visual representation of the command line commands | is a front end graphical interface for apt that gives a visual representation of the command line commands | ||
such as apt-get install [filename]. | such as /* apt-get install [filename] */. | ||
To install a certain package you open the interface main window and search for the package name. Once located | To install a certain package you open the interface main window and search for the package name. Once located | ||
| Line 170: | Line 172: | ||
<center>[[File:mark_window.png]]</center> | <center>[[File:mark_window.png]]</center> | ||
<center><u>Figure | <center><u>Figure 12: Example of Adding a Package using Synaptic Package Manager</u></center> | ||
<p> | <p> | ||
| Line 191: | Line 193: | ||
The first package I looked at was the Web Browser package which is Iceweasel. | The first package I looked at was the Web Browser package which is Iceweasel. | ||
I was originally under the assumption that all Debian distributions would come with Firefox but as I found, from the following | I was originally under the assumption that all Debian distributions would come with Firefox but as I found, from the following | ||
Debian package tracking site | Debian package tracking site, http://packages.debian.org/changelogs/pool/main/i/iceweasel/current/changelog, Firefox is not actually a Debian package. Clearly the maintainers of Ubuntu decided to make it part of their distribution. TAILS instead runs Iceweasel, which is also developed by Mozilla. The version running on TAILS is 3.5.16-10 which is the latest | ||
stable version and has an install size of 3976 Bytes. A new unstable upstream version 8.0 | stable version and has an install size of 3976 Bytes. A new unstable upstream version 8.0 | ||
is available but is not packaged and only in the testing stage. Based on the change log, available | is available but is not packaged and only in the testing stage. Based on the change log, available | ||
| Line 199: | Line 201: | ||
that there has been a large amount of modification as the current package is 9 years older than the | that there has been a large amount of modification as the current package is 9 years older than the | ||
original Phoenix package. This particular package was chosen for this distribution's standard install | original Phoenix package. This particular package was chosen for this distribution's standard install | ||
as it is | as it is modelled on the Mozilla package and is used by most Debian distributions. It also comes preset | ||
with the TOR network functionality which as previously mentioned is what TAILS uses to provide the user | with the TOR network functionality which as previously mentioned is what TAILS uses to provide the user | ||
with online anonymity. In comparison the Debian Ubuntu distributions used in school run Ubuntu 10.04 and | with online anonymity. In comparison the Debian Ubuntu distributions used in school run Ubuntu 10.04 and | ||
| Line 218: | Line 220: | ||
As per the site http://packages.qa.debian.org/v/vidalia.html the latest "stable" version is | As per the site http://packages.qa.debian.org/v/vidalia.html the latest "stable" version is | ||
0.2.10-3. The latest unpackaged upstream version is 0.3.0-alpha. The same site has a link to the | 0.2.10-3. The latest unpackaged upstream version is 0.3.0-alpha. The same site has a link to the | ||
changelog which shows that the package has been modified | changelog which shows that the package has been modified considerably since inception and continues | ||
to be modified in experimental upstream versions. It was originally deployed 3 years ago and has undergone | to be modified in experimental upstream versions. It was originally deployed 3 years ago and has undergone | ||
graphical changes and bug fixes. I am not aware of any other Debian distribution that comes with the Vidalia | graphical changes and bug fixes. I am not aware of any other Debian distribution that comes with the Vidalia | ||
| Line 255: | Line 257: | ||
<p> | <p> | ||
Next I looked at | Next I looked at five of the utilities that come with TAILS and all other Debian distributions, procps (or ps), tar, sudo, mount and lsof. | ||
The utility ps or procps is used to list the current running processes | The utility ps or procps is used to list the current running processes, tar is an archiving utility (compression of files), sudo is a software package used to provide limited super user access privileges, mount is a package used to manipulate file systems and lsof is used to list any open files but | ||
processes currently running on the system. TAILS uses the most current stable versions for | processes currently running on the system. TAILS uses the most current stable versions for all the packages which are | ||
15 years newer than the original packages developed. Most of the changes are related to bug fixes in response to different | 15 years newer than the original packages developed. Most of the changes are related to bug fixes in response to different | ||
versions of the Debian distribution. The packages weren't chosen for TAILS for any special reason only that they are standard | versions of the Debian distribution. The packages weren't chosen for TAILS for any special reason only that they are standard | ||
| Line 279: | Line 281: | ||
<p> | <p> | ||
TAILS uses the same initialization process as most other Debian System-V distributions and as such, after the kernel | TAILS uses the same initialization process as most other Debian System-V distributions and as such, after the boot loader and kernel have executed and the kernel has gone idle, the first process that is run is /sbin/init (part of the sysvinit package) which establishes the user space. | ||
The init script decides which rc*.d files to run. In the case of | The init script decides which rc*.d files to run. In the case of TAILS the rc*.d is a directory that contains symbolic links to the actual files to be run from/etc/init.d. The rc*.d directories are the run levels of the system and define which point of the boot-up the system has entered. System-V systems run these scripts sequentially unlike Upstart systems which can run them in parallel. The init script first runs the S* files linked from rcS.d after which it will go to the initial run-level for the system. For most Debian systems the initial run level(the first one that init searches through) is rc2.d. The run levels rc0.d and rc6.d contain the halt and reboot scripts respectively and as such are only entered when the system needs to reboot or stop a process. By listing the contents of these directories the user will notice that the scripts are prefixed by the letter K and a #. The letter K tells the init script that these processes should be stopped and the # refers to the ascending order they should be stopped in. The other run levels, rc1.d - rc5.d, contain the scripts that init uses to start processes as well as scripts to end processes. The symlinks to the packages to start are prefixed with the letter S and a # (In the case of these run-levels all processes whose symlink start with a K are run before those that start with an S). The letter S tells init to start the process while the # refers to the order in which to start each process in the respective run level. For example, looking into rc2.d we see that init would be required to run the sudo script before it executes the cron script and it would execute both in run level 2. Once all the processes in these levels have been spawned init goes dormant and waits for one of the following 3 events: one of the processes started to end or die, a request from /sbin/telinit to change the run-level or a power failure signal. By looking at the rc#.d directories the user can find out which packages are executed and in which order. In the case of TAILS here are some of the major packages in order of execution. I found them by looking in the rcS.d and rc#.d directories for the symlinks: | ||
</p> | </p> | ||
<p> | <p> | ||
''' | '''rcS.d run-level''' | ||
</p> | </p> | ||
<p> | <p> | ||
1. | 1. procps: contains programs such as ps | ||
</p> | </p> | ||
<p> | <p> | ||
2. | 2. resolvconf: Package used to keep information on DNS up to date. | ||
</p> | </p> | ||
<p> | |||
'''Initial run-level: rc2.d (as defined in /etc/inittab file)''' | |||
</p> | |||
<p> | |||
1. sudo (S01sudo): Allows system admin to give root access to users | |||
</p> | |||
<p> | |||
2. cron (S02cron): This is the package scheduling deamon | |||
</p> | |||
<p> | |||
3. cups(S02cups): This package serves as a replacement for the lpd package and is the printing system | |||
</p> | |||
<p> | <p> | ||
'''run-level: rc6.d''' | |||
</p> | |||
<p> | |||
1. STOP TOR (K02Tor): Stops the tor network | |||
</p> | |||
<p> | |||
Strangely I was unable to find any symlink suggesting the Tor network was ever started on boot up even though it is stopped and there | |||
is a corresponding file in the /etc/init.d tab. The difference between TAILS and the latest versions of Ubuntu is that Ubuntu uses the Upstart system versus the older System-V system. The upstart system allows Ubuntu to run its bootup scripts in parallel over all the run levels. | |||
</p> | |||
<p> | |||
I learnt some of this material from lab 4 but the majority of the information I found on the web from these sites: | I learnt some of this material from lab 4 but the majority of the information I found on the web from these sites: | ||
</p> | </p> | ||
| Line 302: | Line 326: | ||
<p> | <p> | ||
http://www.linfo.org/sbin.html | http://www.linfo.org/sbin.html | ||
</p> | |||
<p> | |||
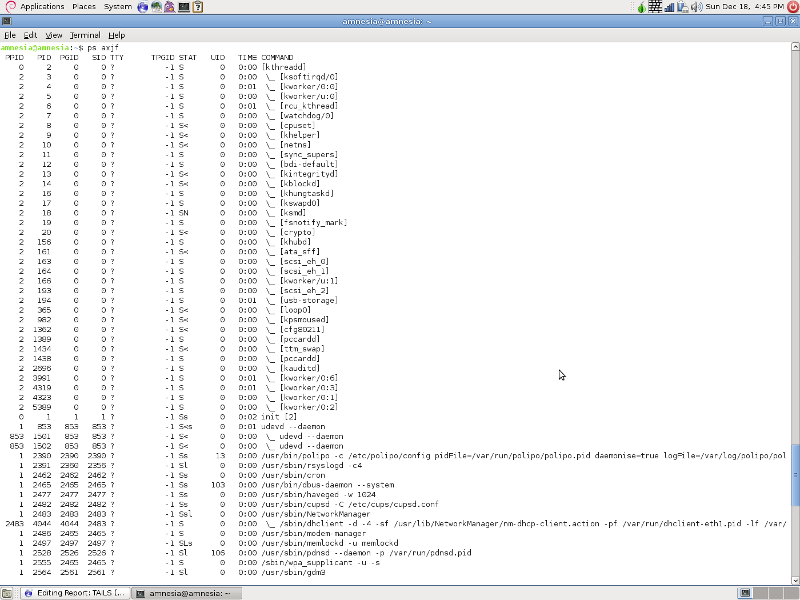
After the system has initialized and the the login process is complete we can take a look at how processes are started during startup and initialization, as well as the currently running processes, by taking a look at the process tree using the ps utility. There are a number of optioins that a user can select to view the process on the system the following output was generated using the /* ps axjf */ command at the command line. | |||
</p> | |||
<center>[[File:Ps_final.png]]</center> | |||
<center><u>Figure 13: Process Tree Output from ps Utility</u></center> | |||
<p> | |||
You can see from this screenshot that the first process to run, aside from the kernel and based on the PID (Process Identifier) number, is init. Init is the parent process for all other programs such as the scheduler, chron (PID 2462), and most of the packages we discussed earlier. The parent process is identified by the Parent Process ID (PPID) field. Although not shown here, the last entry in the process tree is the ps process I used to output the tree. It shows how the ps utility is a child of the bash shell and is executed by the bash process itself just as the bash process is started by the login process which in turn is launched by init. | |||
</p> | </p> | ||
== References == | == References == | ||
http://tails.boum.org/index.en.html | TAILS. Homepage. "TAILS: Privacy for anyone anywhere" <http://tails.boum.org/index.en.html> | ||
https://www.torproject.org/ | TOR. Homepage. "Tor Project: Anonymity Online" <https://www.torproject.org/> | ||
http://distrowatch.com/ | Distrowatch. Homepage. "DistroWatch: Put the fun back into computing. Use Linux, BSD" <http://distrowatch.com/> | ||
http://www. | Gray, John. "The Tails Project's The Amnesic Incognito Live System (Tails)" 16 September 2011 <http://www.linuxjournal.com/content/tails-projects-amnesic-incognito-live-system-tails> | ||
Claws-mail. Homepage. "Claws: The user-friendly, lightweight, and fast email client" <http://www.claws-mail.org/> | |||
Pidgin. Homepage. "Pidgin" <http://developer.pidgin.im/wiki> | |||
https://www.linux.com/news/enterprise/systems-management/8116-an-introduction-to-services-runlevels-and-rcd-scripts | |||
http:// | YoLinux. Homepage. "YoLinux.com: Linux Init Process / PC Boot Procedure" <http://www.yolinux.com/TUTORIALS/LinuxTutorialInitProcess.html> | ||
http:// | Debian Package Tracking System. Homepage. "Debian Package Tracking System" <http://packages.qa.debian.org/common/index.html> | ||
Latest revision as of 22:26, 18 December 2011
PART 1
Background
The distribution is known as The Amnesic Incognito Live System (TAILS). The goal of the distribution is to provide anonymity for the user and thus targets any consumers that require a higher level of privacy when using the Internet and do not want to leave traces of their activity on the host file system. TAILS is an extension of the Debian GNU/Linux distribution system. It is open source but the project started being developed by developers at boum.org although I was unable to find any specific developer names.
To achieve online anonymity, TAILS uses the Tor Network. The Tor Network is an open network that is accessible through free software. Tor is designed to make it difficult for anyone to trace your Internet traffic. It uses a network of virtual tunnels to protect the user from “traffic analysis” (eavesdropping, IP spoofing, ARP spoofing, etc...). To combat these attacks it sends your data packets as multi-hop circuit of relays. Each relay only knows the address of the relay that provided the data and the relay it will provide the data too. This effectively erases the track back to the sender. Any eavesdropper will only be able to trace the message back to the relay before. One drawback is that the Tor network does not encrypt data from relay to relay only from the sender to the first relay and from that relay back to the sender. This prevents the eavesdropper from being able to view your data at the first relay but does not prevent them from viewing your data at other relays. Although the onus is on the website the user is communicating with to provide the end-to-end protection TAILS does provide this protection when using IRC or Email through software that comes with the system. Another drawback is that most if not all modern web browsers use JavaScript, Adobe Flash and cookies, these have been proven to occasionally bypass the anonymity feature. To combat this TAILS provides its own web browser based of Firefox called Iceweasel. Unfortunately some sites will not work with it due to its limitations.
To help protect against leaving traces on the host computer TAILS runs as an independent operating system unless made to do otherwise. TAILS is a Livedistro that runs off a bootable USB or CD (USB is faster) requiring no installation on the host PC. The only memory TAILS accesses is RAM which is overwritten on PC shutdown (unless the shutdown is abrupt, such as in a power failure) leaving no trace on the system. If you choose to do so you can run TAILS through as a virtual machine but this negates the above protection feature as both the virtual machine and the host OS will leave traces on the host PC. The other drawback is that as you are not using the host PC file storage system you need to use a separate storage system such as another USB drive to save any data that you work on while in TAILS.
TAILS can be obtained for free from the Internet. The latest version is 0.8.1 and it was released on October 16th, 2011. It downloads as an ISO image of 579 Mb in size. The home website for TAILS has an interesting feature where it allows the user to verify that the ISO they downloaded is authentic as the genuine version is encoded with a cryptographic signature. The user can either do this through a check through Firefox, using an add-on, or through software known as Gpg4win which is essentially an encryption and decryption software. This just shows the level of commitment the developers have to user privacy and security.
Installation/Startup
Once the user has downloaded the ISO image they will need to make the USB or CD key boot from that ISO. I used the USB approach and used the Universal USB Installer software (version 1.8.6.8). The software provides you a main window where the user selects the type of distribution, the location of the ISO file and selects the USB key drive letter from a drop down menu. The user can also format the key during the setup process. After creating the USB key, users simply make the host PC boot to the USB upon startup. You will be presented with a boot menu where you can select your preferred language. The distribution system then loads the desktop UI and TAILS automatically launches an Iceweasel session window and tests the TOR connection.
The actual start-up of the distribution system from the USB key was very fast. The load time was approximately 30-45 seconds after choosing the language at the boot menu. As TAILS is meant to run as a Livedistro system I did not use any virtualization software to get it running (although the option is there if you so choose) and as such do not have a screen shot of the actual loading process.
Basic Operation
The first impression is that TAILS is much like any Debian based distribution system. The desktop looks very similar as it contains the same status bar on the bottom of the screen and the menu bar up top, however compared to say the latest version of Ubuntu, TAILS does not come preloaded with many applications.
As TAILS first runs a web browser to TOR to test the network connection it provides you with the falsified IP address your system uses when on the network. Checking the TAILS distribution using /* ifconfig */ it showed that the IP addresses did not match up.
To essentially control how you use the TOR network TAILS provides software known as Vidalia (pictured as an onion in the top right hand corner of the UI). The application is automatically launched once the system connects to a network. To open the control panel double click the icon. Once the control panel is opened the user can do the following:

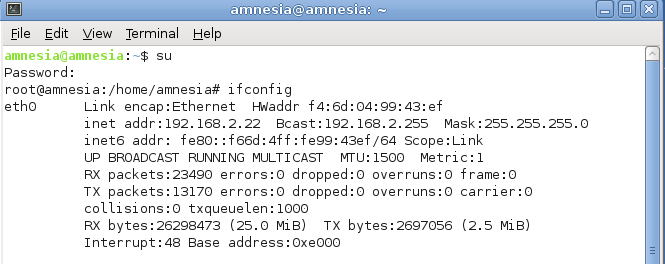
• View the Tor network: This shows a list of relays, currently used routes and their status
• Choose a new identity to use: Tears down all current circuits and creates new ones. Your route is modified into a new one.
• View the bandwidth graph: This allows the user to check the current bandwidth usage on their circuit.
• Connect through a bridge: If your ISP prevents you from using the Tor network you can “bridge” into the Tor network using Vidalia by going to the settings, network and then selecting the “My ISP blocks connections to the Tor network” checkbox. This will bring you to a form to add a Tor bridge as an entry point.
• Setting up a Tor relay: Vidalia gives the user the option of setting themselves up as a Tor relay to help the Tor network.
• Message Log: Acts as an event viewer for the Tor network. Displays messages such as if the Tor software is running and if there is a dangerous connection
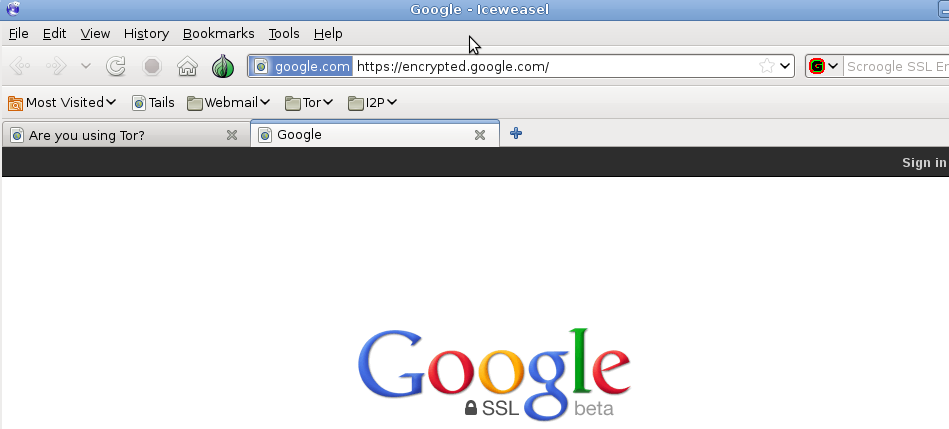
When using the web browser Iceweasel you will notice that all connections that can be encrypted are through SSL. The indication is in the address name of the website which starts with https:// instead of the usual http:// (the s standing for secure). I found that web browsing was slower than usual due to the relay of packets through the Tor network.
The only problem I ran into upon start-up was a functionality issue as even though TAILS runs of GNOME very little of the utilities were actually present including gnome-screenshot. It was necessary to install the utilities. Besides that the only other issue I experience with the initial setup and while trying some of TAILS’s features was the noticeable lag when trying to connect to websites.
Usage Evaluation
In the end I found TAILS to be quite similar to most Debian distributions I have used. The extra security features are interesting to explore. I do find that TAILS goes well beyond the other distributions I’ve played with when it comes to security as is evident by its focus on end-to-end encryption, use of the Tor network and refusal to leave traces on the host OS. The only issue is the lack in speed when using the Tor network to connect to websites but if the user is willing to forgo the entire purpose of TAILS they can download a normal Web Browser such as Firefox.
PART 2
Software Packaging
As TAILS is modelled off Debian GNU/Linux distribution it uses the Debian (*.deb) packaging format for its software. TAILS comes preloaded with some of the usual software packages such as OpenOffice.org, Iceweasel and GNOME-terminal. In total TAILS comes preloaded with 1096 packages as is shown by the Synaptic Package Manager main window, which is a front end GUI to dpkg. TAILS uses the Advanced Packaging Tool (APT) system to manage the installation and removal of software. It is a front end user interface for the dpkg package utility. Where dpkg is used on individual packages the apt tools in the apt package (such as apt-get) manage the relations between the packages. I primarily used the man page for dpkg to find the necessary information.
To get a list of the packages that are installed the user can search the /var/log/dpkg.log file with the following command: /* more /var/log/dpkg.log */
This will provide the user with a list of when a certain software package was installed, removed or updated. The user can also type /* dpkg -l */ at the commnd prompt. This will provide the user with a list of installed packages in alphabetical order as well as the access rights associated to them.
For more in depth information on the packages such as the install-size, version, dependencies and description the user can view the /var/lib/dpkg/status file.
To add and remove packages the user would use the apt-get package mentioned earlier. To insatll a package the user would type the following command: /* apt-get install [package_name] */. The user can specify more than one package at a time. To remove packages the user would type the following command at the command line prompt: apt-get remove [filename]. As with install the user can specify more than one filename. A set of options are available in conjunction with these commands such as, -d which specifies to only download the package. Unfortunately for TAILS this function does not seem to work. There is always an error: Unable to locate package [filename].
I checked the /etc/apt/sources.list file which contains the locations that apt checks to download the packages. the output is consistent with an Ubuntu distribution installation:
To install the packages I had to use the Synaptic Package Manager utility that comes available with TAILS. This is a front end graphical interface for apt that gives a visual representation of the command line commands such as /* apt-get install [filename] */. To install a certain package you open the interface main window and search for the package name. Once located you select the package and double click. You will presented with a window requesting you mark the package for install.
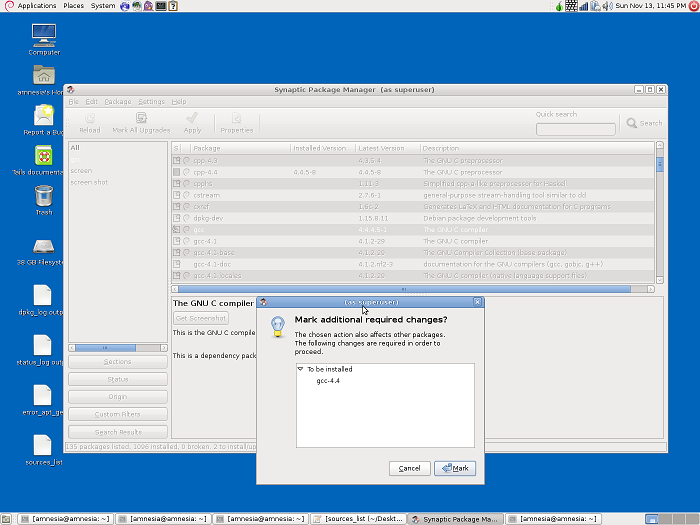
Once the package has been marked for install the user clicks the "Apply" button in the toolbar and the package is installed.
The software catalog for tails is as extensive as all Debian distribution catalogs. In total there are 37742 packages available for installation listed by the Synaptic Package Manager utility.
Major Package Versions
The following section describes some of the major packages available in TAILS.
The first package I looked at was the Web Browser package which is Iceweasel. I was originally under the assumption that all Debian distributions would come with Firefox but as I found, from the following Debian package tracking site, http://packages.debian.org/changelogs/pool/main/i/iceweasel/current/changelog, Firefox is not actually a Debian package. Clearly the maintainers of Ubuntu decided to make it part of their distribution. TAILS instead runs Iceweasel, which is also developed by Mozilla. The version running on TAILS is 3.5.16-10 which is the latest stable version and has an install size of 3976 Bytes. A new unstable upstream version 8.0 is available but is not packaged and only in the testing stage. Based on the change log, available at the Debian package tracking site above, Iceweasel has undergone a considerable amount of package modification and it continues to with the latest experimental and unstable releases. The webpage shows how Iceweasel has grown from the original Phoenix web browser to the Mozilla-firebird web browser then to Firefox 2.0 and finally Icewesel itself. It is obvious that there has been a large amount of modification as the current package is 9 years older than the original Phoenix package. This particular package was chosen for this distribution's standard install as it is modelled on the Mozilla package and is used by most Debian distributions. It also comes preset with the TOR network functionality which as previously mentioned is what TAILS uses to provide the user with online anonymity. In comparison the Debian Ubuntu distributions used in school run Ubuntu 10.04 and actually use Mozilla Firefox.
The next packages I chose to explore were the UI packages for email, chat and TOR networking (Claws-mail, Pidgin and Vidalia respectively). The reason I chose these packages is that they appear to be independent to TAILS as they concentrate on security and user anonymity which is the overall goal of TAILS.
i) Vidalia: GUI for managing the TOR network
The package has an install size of 5264 Bytes. The version is 0.2.14-1 which is an unstable version. As per the site http://packages.qa.debian.org/v/vidalia.html the latest "stable" version is 0.2.10-3. The latest unpackaged upstream version is 0.3.0-alpha. The same site has a link to the changelog which shows that the package has been modified considerably since inception and continues to be modified in experimental upstream versions. It was originally deployed 3 years ago and has undergone graphical changes and bug fixes. I am not aware of any other Debian distribution that comes with the Vidalia package, certainly not the one's at school that run Ubuntu 10.04, nor could I find another similar package run by another Debian distribution and am therefore not capable of making comparisons. The reason why this package was chosen as a standard install for this distribution is that it is a GUI used by the user to manage connectivity to the TOR network.
ii) Pidgin: GUI for messaging client.
The package was initially developed and deployed under the name Gaim in 1998. It has undergone considerable modifications in that time and evolved into Pidgin. Pidgin provides the ability to encrypt your chat sessions using encryption such as RSA which is why it would have been chosen for this distribution who's goal is user security as mentioned before. The version is 2.7.3-1+squeeze according to the site http://packages.qa.debian.org/p/pidgin.html is the latest stable version and has an install size of 2060 bytes. The latest non packaged upstream version is 2.10.0-1. In the labs at Carleton we have the option to use emesene as a chat client. The two programs are different in the sense that Pidgin has security plugins available as the Pidgin encryption mentioned above where as emesene does not provide these features or plugins. Clearly Pidgin is the better choice for a distribution intent on user security and privacy.
iii) Claws-mail: GUI for e-mail
The email client that comes installed with TAILS is Claws-mail. Claws-mail originated from the package sylpheed-claws-gtk2 which was created in 2004. The version run by TAILS is the latest stable version. The reason why this package would have been chosen for this distribution is again for it's security plugins. There is a plugin available to allow PGP encryption of data. I know of other distributions that still use sylpheed instead of Claws as it is a much more stripped down and light weight client making it ideal for lightweight distributions such as Swift which is also based of the Debian Linux/GNU distribution.
Next I looked at five of the utilities that come with TAILS and all other Debian distributions, procps (or ps), tar, sudo, mount and lsof. The utility ps or procps is used to list the current running processes, tar is an archiving utility (compression of files), sudo is a software package used to provide limited super user access privileges, mount is a package used to manipulate file systems and lsof is used to list any open files but processes currently running on the system. TAILS uses the most current stable versions for all the packages which are 15 years newer than the original packages developed. Most of the changes are related to bug fixes in response to different versions of the Debian distribution. The packages weren't chosen for TAILS for any special reason only that they are standard packages for a Debian distribution. The packages are identical to the ones run on the Ubuntu systems at school.
Finally I took a look at the shell package that comes with TAILS. As tails is based on the Debian GNU/Linux distribution it uses the bash shell for the OS. TAILS runs the latest stable version (4.1-3) which was released 15 years after the original version was deployed. Many of the modifications are related to bug fixes with respect to different versions of Debian distributions. In comparison the Ubuntu 10.04 Debian distributions in the school, when initially started, run the csh shell by default. This shell is considerably smaller in logical size and is a more stripped down version of bash as it lacks the capabilities such as command line editing using Vi. The csh shell was deployed the same year as the bash shell however TAILS does not provide a csh shell.
Initialization
The following section will describe the initialization process for TAILS.
TAILS uses the same initialization process as most other Debian System-V distributions and as such, after the boot loader and kernel have executed and the kernel has gone idle, the first process that is run is /sbin/init (part of the sysvinit package) which establishes the user space. The init script decides which rc*.d files to run. In the case of TAILS the rc*.d is a directory that contains symbolic links to the actual files to be run from/etc/init.d. The rc*.d directories are the run levels of the system and define which point of the boot-up the system has entered. System-V systems run these scripts sequentially unlike Upstart systems which can run them in parallel. The init script first runs the S* files linked from rcS.d after which it will go to the initial run-level for the system. For most Debian systems the initial run level(the first one that init searches through) is rc2.d. The run levels rc0.d and rc6.d contain the halt and reboot scripts respectively and as such are only entered when the system needs to reboot or stop a process. By listing the contents of these directories the user will notice that the scripts are prefixed by the letter K and a #. The letter K tells the init script that these processes should be stopped and the # refers to the ascending order they should be stopped in. The other run levels, rc1.d - rc5.d, contain the scripts that init uses to start processes as well as scripts to end processes. The symlinks to the packages to start are prefixed with the letter S and a # (In the case of these run-levels all processes whose symlink start with a K are run before those that start with an S). The letter S tells init to start the process while the # refers to the order in which to start each process in the respective run level. For example, looking into rc2.d we see that init would be required to run the sudo script before it executes the cron script and it would execute both in run level 2. Once all the processes in these levels have been spawned init goes dormant and waits for one of the following 3 events: one of the processes started to end or die, a request from /sbin/telinit to change the run-level or a power failure signal. By looking at the rc#.d directories the user can find out which packages are executed and in which order. In the case of TAILS here are some of the major packages in order of execution. I found them by looking in the rcS.d and rc#.d directories for the symlinks:
rcS.d run-level
1. procps: contains programs such as ps
2. resolvconf: Package used to keep information on DNS up to date.
Initial run-level: rc2.d (as defined in /etc/inittab file)
1. sudo (S01sudo): Allows system admin to give root access to users
2. cron (S02cron): This is the package scheduling deamon
3. cups(S02cups): This package serves as a replacement for the lpd package and is the printing system
run-level: rc6.d
1. STOP TOR (K02Tor): Stops the tor network
Strangely I was unable to find any symlink suggesting the Tor network was ever started on boot up even though it is stopped and there is a corresponding file in the /etc/init.d tab. The difference between TAILS and the latest versions of Ubuntu is that Ubuntu uses the Upstart system versus the older System-V system. The upstart system allows Ubuntu to run its bootup scripts in parallel over all the run levels.
I learnt some of this material from lab 4 but the majority of the information I found on the web from these sites:
http://www.linfo.org/sbin.html
After the system has initialized and the the login process is complete we can take a look at how processes are started during startup and initialization, as well as the currently running processes, by taking a look at the process tree using the ps utility. There are a number of optioins that a user can select to view the process on the system the following output was generated using the /* ps axjf */ command at the command line.
You can see from this screenshot that the first process to run, aside from the kernel and based on the PID (Process Identifier) number, is init. Init is the parent process for all other programs such as the scheduler, chron (PID 2462), and most of the packages we discussed earlier. The parent process is identified by the Parent Process ID (PPID) field. Although not shown here, the last entry in the process tree is the ps process I used to output the tree. It shows how the ps utility is a child of the bash shell and is executed by the bash process itself just as the bash process is started by the login process which in turn is launched by init.
References
TAILS. Homepage. "TAILS: Privacy for anyone anywhere" <http://tails.boum.org/index.en.html>
TOR. Homepage. "Tor Project: Anonymity Online" <https://www.torproject.org/>
Distrowatch. Homepage. "DistroWatch: Put the fun back into computing. Use Linux, BSD" <http://distrowatch.com/>
Gray, John. "The Tails Project's The Amnesic Incognito Live System (Tails)" 16 September 2011 <http://www.linuxjournal.com/content/tails-projects-amnesic-incognito-live-system-tails>
Claws-mail. Homepage. "Claws: The user-friendly, lightweight, and fast email client" <http://www.claws-mail.org/>
Pidgin. Homepage. "Pidgin" <http://developer.pidgin.im/wiki>
YoLinux. Homepage. "YoLinux.com: Linux Init Process / PC Boot Procedure" <http://www.yolinux.com/TUTORIALS/LinuxTutorialInitProcess.html>
Debian Package Tracking System. Homepage. "Debian Package Tracking System" <http://packages.qa.debian.org/common/index.html>